Resuming from Dormancy
Confluence — RFC / Runbook
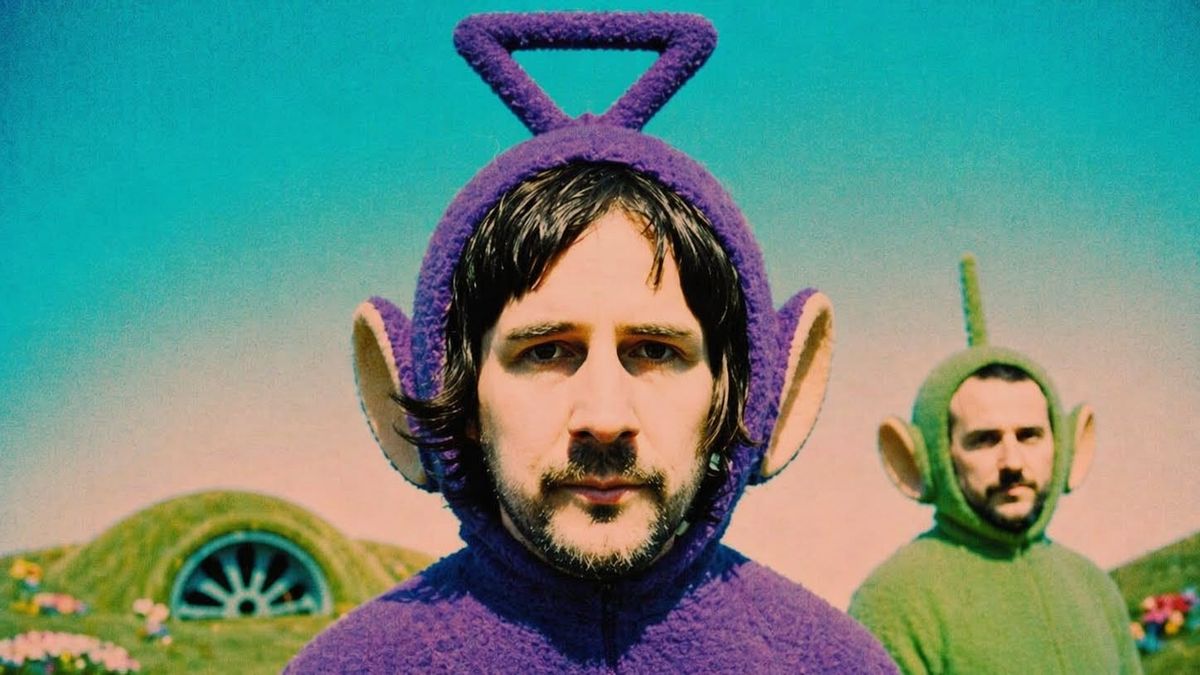
Service: Boards of Canada
Release: Inferno (May 29, 2026)
Owner: Warp Records
Region: boc-west-1 (long-lived)
Status: RESUMED (from dormancy)
0) TL;DR
A long-dormant, stateful service has resumed execution without formal restart logs. Deployment uses artifact seeding (VHS + posters) instead of conventional announcement channels. New workload (Inferno, 18 tasks) scheduled for late May. System behavior is consistent with prior releases: low observability, high signal integrity, strict “no-out-of-band-comms” policy.
1) Background
- Last stable release: Tomorrow’s Harvest (2013)
- Dormancy window: ~13 years (no public writes; read traffic remained high)
- Historical deployment pattern:
- pre-release obfuscation (ARG-like breadcrumbs)
- physical artifact propagation (low-bandwidth, high-signal)
- delayed convergence into a canonical object (LP/CD/digital)
Key property: Service never truly “down”; ran as zombie PID with periodic fan-driven keepalives.
2) Incident Classification
Type: Planned reactivation disguised as anomaly
Severity: SEV-0 (global attention; expected)
User Impact: Positive (curiosity spike, increased traffic to Warp/Bleep)
Blast Radius: Worldwide (poster sightings across multiple metros)
3) Detection Signals
Observed indicators prior to official acknowledgment:
- Unsolicited VHS artifacts delivered to trusted endpoints (Bleep customers)
- Emergent hexagonal logo (new namespace)
- Distributed poster drops (London, Tokyo, NYC, LA)
- Social chatter forming a pattern-recognition mesh
Detection method: Human-in-the-loop anomaly detection (fans)
False positives: None meaningful (high confidence signature)
4) Deployment Strategy
Model: Edge-seeded, pull-based convergence
- Seed physical artifacts → low-noise channels
- Allow community nodes to correlate signals
- Delay central confirmation
- Publish canonical object (album) across formats:
- red translucent double LP (+ booklet)
- CD
- digital
Why it works:
- Bypasses algorithmic feeds (no reliance on ranking systems)
- Increases engagement latency (people look)
- Preserves brand invariants: mystery, degradation, discovery
5) Architecture (Conceptual)
[Analog Artifacts] --> [Human Pattern Matching] --> [Social Propagation]
| |
v v
[Low Fidelity] [High Curiosity]
\___________________________________________/
|
v
[Canonical Release: Inferno]
Notes:
- System intentionally mixes low-fidelity inputs with high-attention outputs
- No central dashboard; observability is by design incomplete
- Control plane remains opaque
6) Configuration & Constraints
- Observability: Minimal (no interviews, sparse metadata)
- Change Management: Manual, infrequent, high-impact
- Backwards Compatibility: Strong (aesthetic + method preserved)
- Throughput: Low (long release cycles)
- Consistency Model: Eventual (fans assemble meaning over time)
7) Risk Assessment
Primary risks:
- Canon lock-in: System now perceived as a “monument,” reducing tolerance for deviation
- Overfit expectations: Users expect prior behavior; novelty penalized
- Signal dilution: Wider audience may misinterpret obfuscation as marketing gimmick
Mitigations:
- Continue artifact-first approach (keeps signal distinctive)
- Maintain sparse comms (avoid over-explanation)
- Lean into internal vocabulary (track titles suggest continuity, not reboot)
8) What’s New in Inferno (Speculative)
Based on published task list (18 tracks):
- Continued emphasis on time/decay primitives (“Deep Time,” “Memory Death”)
- System-level themes (“The Process,” “All Reason Departs”)
- Boundary traversal (“You Retreat In Time And Space”)
Interpretation: Not a new service; extension of existing API with deeper endpoints.
9) Runbook — How to Consume
Goal: Maximize signal fidelity; minimize noise.
- Prefer full-album execution on first pass (sequential, no shuffle)
- Use low-distraction environment (reduce competing processes)
- Avoid pre-reading reviews (prevents bias injection)
- After baseline run, pin key properties (tracks) for repeated calls
Anti-patterns:
- Skipping directly to “top tracks” (premature optimization)
- Treating release as a one-shot event (system rewards iteration)
10) Post-Release Tasks
- Compare instances against prior versions (Music Has the Right to Children, Geogaddi, Tomorrow’s Harvest)
- Identify new properties that persist across listens (methods worth calling)
- Update personal “SD card deployment” (prune/archive as needed)
11) Open Questions
- Is Inferno a new hinge (architecture change) or optimization pass?
- Does artifact seeding scale in a fully algorithmic ecosystem?
- Will observability increase post-release, or remain intentionally degraded?
12) Appendix: Known Invariants
- No “official narrative” provided
- Meaning assembled by listeners, not declared by maintainers
- Artifacts precede explanation
- The process never truly stops — it idles
Final Note
This system does not follow typical DevOps best practices.
It violates:
- rapid iteration
- high observability
- clear documentation
…and yet maintains one of the most stable long-term SLAs in the domain.
Conclusion: Not all resilient systems are optimized for visibility. Some are optimized for persistence.